HIPAA-Compliant Meeting Recording: A Developer's Guide
A telehealth platform adds video consultation recording so physicians can review patient interactions for quality improvement. The engineering team deploys a meeting recording bot, stores the transcripts in their existing database, and ships the feature. Six months later, a HIPAA audit finds that the recording pipeline lacks encryption at rest, access controls are insufficiently granular, and there's no Business Associate Agreement with the recording vendor. The result: a corrective action plan, significant remediation costs, and a delay to the product roadmap.
This scenario is common because HIPAA compliant meeting recording looks straightforward at the API level, you're just recording a video call but the compliance requirements create specific technical obligations that aren't obvious until you're being audited. For developers building healthcare applications that include any form of meeting or call recording, understanding exactly what HIPAA requires and how to implement it is foundational, not optional.
This guide covers what makes a meeting recording subject to HIPAA, the specific Technical Safeguards you need to implement, Business Associate Agreement requirements, data retention policies under HIPAA, and how to design your recording infrastructure with these requirements built in from the start. It's written for developers building healthcare applications, not compliance officers, the goal is to translate regulatory requirements into specific technical decisions.
One important note before we begin: this guide provides technical implementation context but is not legal advice. Your organization's HIPAA compliance program should be overseen by a qualified Privacy Officer, and specific compliance determinations should involve legal counsel familiar with HIPAA.
When Does a Meeting Recording Become PHI?
Protected Health Information (PHI) is individually identifiable health information. Under HIPAA, PHI includes any information that relates to a person's past, present, or future physical or mental health condition, the provision of health care to the individual, or the past, present, or future payment for health care, when that information identifies or could reasonably identify the individual.
A meeting recording becomes PHI when it contains a combination of a health condition and an identifier. An identifier under HIPAA is broad: names, geographic data more specific than state, dates (other than year) related to an individual, phone numbers, email addresses, and 15 other categories. In practice, almost any video or audio recording of a patient consultation contains multiple identifiers (the patient's name and voice, at minimum) and health condition information. The recording is PHI.
Less obvious cases: a physician staff meeting where patient cases are discussed by name is PHI. A training recording that uses real patient cases (even without names visible) may be PHI if the content could identify the patient. Internal quality assurance calls reviewing specific patient complaints may be PHI.
The cleaner analysis is to assume that any recording involving identified or identifiable patients discussing health conditions is PHI, and apply the full Technical Safeguards framework. Attempting to reason whether a specific recording is "probably not PHI" creates compliance risk without proportionate benefit.
HIPAA Technical Safeguards for Meeting Recordings
The HIPAA Security Rule (45 CFR § 164.312) specifies Technical Safeguards that covered entities and their business associates must implement for electronic PHI. Applied to meeting recordings, the requirements translate to four implementation areas.
Access Control (§ 164.312(a)(1)): Each user who can access PHI recordings must have unique identification. Access must be limited to what each role requires (minimum necessary standard). Emergency access procedures must exist. Automatic logoff after inactivity should be implemented for interfaces displaying PHI.
In technical terms: row-level access control on your recordings database scoped to the patient's care team and authorized administrators. No public URLs or shared links for recording files. Authentication required for all recording access. An access log table recording every retrieval with user ID, timestamp, and access type.
Audit Controls (§ 164.312(b)): Hardware, software, and procedural mechanisms must record and examine activity in information systems that contain or use PHI. This is the audit log requirement: every creation, read, update, and deletion of a recording or transcript must be logged in a tamper-evident store. The log must record who took the action, what action was taken, on which record, and when.
Integrity (§ 164.312(c)(1)): Electronic PHI must be protected from improper alteration or destruction. For recordings, this means verifiable integrity: compute a cryptographic hash of the recording at storage time, store the hash separately, and verify it before producing the recording in a clinical or legal context. A mismatch indicates the recording was altered, which is both a HIPAA violation and potentially a serious clinical or legal problem.
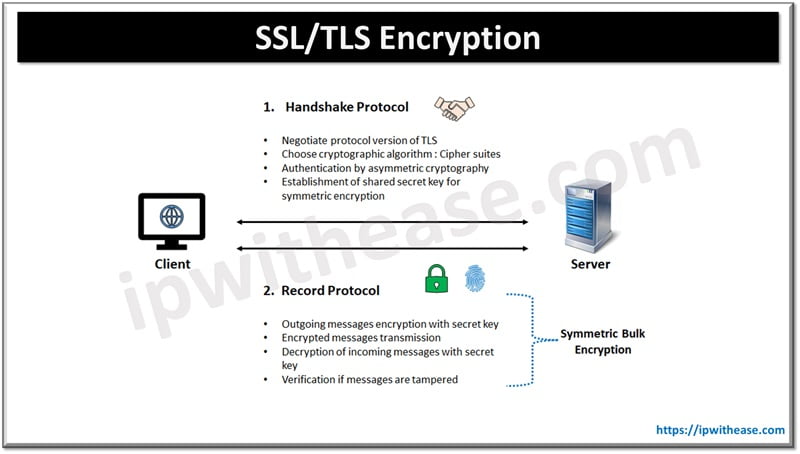
Transmission Security (§ 164.312(e)(1)): Technical security measures must guard against unauthorized access to PHI during transmission over electronic communications networks. In practice: TLS 1.2 or higher for all API communications, for download URLs for completed recordings, and for any interface that displays transcripts. Verify certificate validity. Don't accept self-signed certificates in production code paths that handle PHI.
Encryption at Rest Requirements
Encryption at rest is an Addressable specification under HIPAA, not a Required one, which means it must be implemented unless an organization can document that an equivalent alternative measure is in place. In practice, any organization that stores patient recordings without encryption at rest will have a very difficult time justifying that decision to an auditor. Treat encryption at rest as required.
For recordings stored in cloud object storage: use SSE-KMS (server-side encryption with AWS Key Management Service customer-managed keys, or the equivalent in GCP Cloud KMS or Azure Key Vault). Customer-managed keys are preferable to service-managed keys because they give you control over key rotation and access, and the key usage can be audited independently of the storage service.

For transcript data stored in a database: column-level or full database encryption depending on your database platform. PostgreSQL with pgcrypto or application-level encryption of PHI fields before storage. Document your encryption approach in your HIPAA risk analysis, auditors look for evidence that encryption decisions were made intentionally, not by default.
Encryption key management is often the weakest point. The encryption is only as strong as the key security. Use a dedicated key management service, enforce key rotation policies (annual rotation is common), restrict key access to the application service account and compliance administrators, and log all key usage.
Business Associate Agreements
A Business Associate under HIPAA is any person or entity that performs functions or activities on behalf of a covered entity that involve the creation, receipt, maintenance, or transmission of PHI. Any vendor whose service handles PHI, including a meeting recording API if it stores or transmits PHI, is a business associate.
A Business Associate Agreement (BAA) is a legally required contract between a covered entity and a business associate that establishes what the BA can do with PHI, how they will protect it, and what they will do in the event of a breach. You cannot legally use a service that handles your patients' PHI without a signed BAA in place.
For meeting recording specifically: if the recording passes through or is stored on the vendor's infrastructure, even transiently, a BAA is required. This applies to your meeting recording API, your cloud storage provider, your database hosting service, and your LLM API if you're sending transcripts for processing.
When evaluating vendors for healthcare recording products, ask explicitly: "Do you offer a HIPAA BAA?" and "What are the terms of your BAA?" Some vendors offer BAAs only on enterprise plans. Some have BAA terms that are inconsistent with your compliance requirements. Verify before building on a vendor rather than discovering the BAA situation after a compliance audit.
Retention Policies for HIPAA Meeting Recordings
HIPAA's retention requirements for medical records are 6 years from the date of creation or from when it was last in effect, whichever is later, for covered entities' HIPAA-related documentation. However, medical record retention requirements under state law often extend this: many states require 10 years for adult patient records. Apply the longer of the federal and applicable state retention requirement.
Technical implementation: when creating a bot for a healthcare call via POST https://api.meetstream.ai/api/v1/bots/create_bot, set recording_config with the appropriate retention period. When the audio.processed webhook fires and you download the recording to your infrastructure, write a retention record: file ID, patient ID (if applicable), recording date, and calculated deletion date. A scheduled job runs daily to check for recordings that have passed their retention date and either deletes them or flags them for authorized deletion review.
Don't confuse "minimum retention" with "maximum retention." HIPAA sets minimum retention floors, but organizations can retain longer. Many do retain indefinitely for certain record types. Whatever your policy, document it, apply it consistently, and implement it as automated policy rather than manual process.
De-Identification for Secondary Use Cases
Sometimes you want to use meeting recordings or transcripts for purposes that don't require PHI, training a transcription model, building a quality scoring classifier, or analyzing aggregate communication patterns. Under HIPAA, de-identified data is not subject to the Privacy Rule's restrictions, which means de-identified transcripts can be used more freely.
HIPAA specifies two approaches to de-identification. The Expert Determination method: a statistical or scientific expert determines that the risk of identification is very small and documents the methods. The Safe Harbor method: all 18 specified identifier categories are removed from the data.
For transcript de-identification, the Safe Harbor approach is more practical to implement systematically. The 18 identifiers include names, geographic data more specific than state, all dates except year, phone numbers, email addresses, social security numbers, medical record numbers, account numbers, and several others. A de-identification pipeline runs the transcript through an NLP named entity recognition model that detects and redacts these categories, replacing them with category placeholders: "[NAME]", "[DATE]", "[PHONE]".
State-of-the-art NER models (spaCy, Stanza, and custom fine-tuned models) handle common identifier categories well but miss some edge cases, particularly in medical contexts where identifiers might be embedded in clinical terminology. Validate your de-identification pipeline on a sample of real transcripts and have a clinician or privacy officer review the output before treating it as reliably de-identified. False negatives in de-identification, leaving an identifier in when you thought you removed it, create HIPAA risk.
Developer Responsibilities vs. Infrastructure Responsibilities
For developers building healthcare meeting API applications, the responsibility split is important to understand:
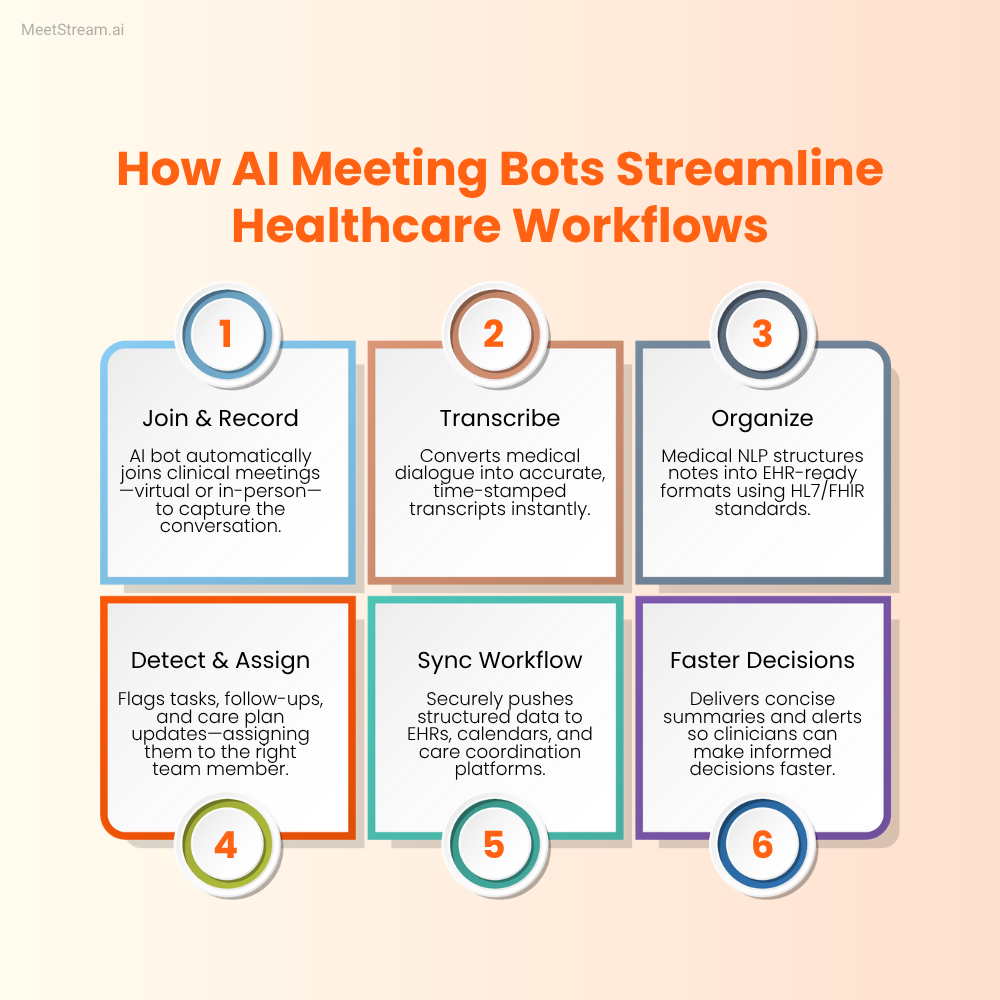
The meeting recording API (MeetStream in this context) provides: reliable bot join across Google Meet, Zoom, and Teams; audio and video recording; speaker-attributed transcription; webhook delivery of recording and transcript artifacts. It handles the capture layer.

Your application is responsible for: BAA execution with all vendors, encryption at rest implementation, access control and audit logging, retention period enforcement, de-identification pipelines for secondary use, disclosure to patients that recording is occurring, and the overall HIPAA compliance program. The recording API is infrastructure. HIPAA compliance is a property of your system's design and operations, not a feature any single vendor provides.
HIPAA compliance requires a written risk analysis, written policies, documented training, and incident response procedures in addition to the technical controls. The technical controls described in this post are necessary but not sufficient, they need to exist within an organizational HIPAA program to satisfy audit requirements.
Frequently Asked Questions
Does a telehealth platform need a BAA with their meeting recording vendor?
Yes. If the meeting recording vendor processes, stores, or transmits patient communications, even temporarily, they are a business associate under HIPAA and a BAA is required. This applies even if the recordings only pass through the vendor's servers transiently before being delivered to your storage. "Transient" storage is still PHI processing. Before integrating any meeting recording API into a healthcare product, confirm that the vendor offers a HIPAA BAA and execute it before processing any patient recordings.
What's the difference between HIPAA's Required and Addressable implementation specifications?
Required specifications must be implemented. Addressable specifications must be implemented unless the covered entity can document that the specification is not reasonable and appropriate, and implement an equivalent alternative measure. In practice, most Addressable specifications, including encryption at rest, automatic logoff, and audit controls for transmission, are implemented by any reasonable security program. The Addressable designation allows flexibility in how they're implemented, not whether they're implemented. Healthcare developers should treat both Required and Addressable specifications as implementation targets.
How do you handle HIPAA compliance when using an LLM API to summarize patient call transcripts?
If you're sending transcripts containing PHI to an LLM API for summarization, that LLM provider is processing PHI and requires a BAA. Major LLM providers have different policies: some (like Azure OpenAI with appropriate configuration) offer HIPAA BAAs. Others do not offer BAAs or require enterprise contracts for BAA eligibility. Evaluate whether the BAA terms are consistent with your compliance requirements before using any LLM API with patient transcripts. Alternatively, de-identify transcripts before sending to LLM APIs, removing identifiers as described above means the data sent to the LLM is no longer PHI and doesn't require a BAA.
What audit log entries are required for HIPAA compliance around meeting recordings?
The HIPAA Security Rule requires that audit controls record activity in systems containing PHI, but doesn't specify exact log fields. Best practice based on HIPAA audit guidance is: action type (create/read/update/delete), timestamp, user ID, session ID, record identifier (recording ID, transcript ID), and outcome (success/failure). For recordings specifically, also log: who initiated the recording, who has been granted access, and any downloads or exports of the recording file. These logs should be retained for at least the same period as the recordings themselves and stored in a tamper-evident format, use an append-only database table or a dedicated logging service rather than a mutable log file.
Can meeting recordings be used for medical AI training while maintaining HIPAA compliance?
Yes, through two paths. First, with patient authorization: explicit written authorization from patients for secondary use of their health information. Second, through de-identification: recordings and transcripts that have been reliably de-identified under HIPAA's Safe Harbor or Expert Determination standards are no longer PHI and can be used without restriction. The de-identification approach is more scalable for training data generation but requires rigorous validation of the de-identification pipeline. Institutional Review Board review may also be required depending on the nature of the research use, which is a separate consideration from HIPAA compliance.
If you're building a hipaa meeting transcription product, start with your vendor BAA stack before writing application code. The MeetStream API documentation covers recording configuration and webhook event handling. Technical implementation details are straightforward once your compliance framework is in place. The MeetStream team can discuss BAA requirements for healthcare use cases directly.




